Onion links represent a unique method of accessing information on the dark web. These layered links are designed to conceal the true destination, making them impervious to track. Navigating onion links requires specialized software like Tor, which secures your connection and conceals your presence. The nature of these links often makes them associated with illicit activities, but they also offer a platform for private communication and access to suppressed information.
- Discovering onion links can be a challenging process, requiring specialized knowledge.
- The privacy offered by onion links is a double-edged sword, as it can be used for both legitimate and criminal purposes.
Delving into the Secrets of Tor's Hidden Web
Tor's hidden web, often referred to as the Darknet, is a realm shrouded in mystery and intrigue. This digital underworld operates on a anonymous network, providing users with a shield of privacy and security. Tucked away this labyrinthine network lie hidden services, offering everything from illicit goods and services to safe spaces.
Accessing the hidden web requires specialized applications like the Tor browser, which masks your traffic, making it highly challenging to trace. Due to this heightened level of anonymity, the hidden web has become a hotbed for shadowy dealings.
Nonetheless, it's important to note that not every on the hidden web is nefarious. There are also lawful uses for Tor, such as protecting whistleblowers in countries with restrictive governments.
Venturing into the Darknet: A Guide to Onion Links
The dark web, a clandestine realm shrouded in onionlinks anonymity, is often linked with illicit activities. However, it's also home to platforms that champion independence. To access these hidden corners of the internet, you'll need to navigate through onion links, special URLs that employ the Tor network for enhanced encryption.
Onion links are marked by their unique design, resembling a string of .onion domains. These addresses can be obtained through various channels, including specialized forums and hidden services within the Tor network itself. Be aware that venturing into the dark web carries inherent risks, as it's a space where illegal activity can proliferate. Exercise caution, utilize strong security measures, and never share sensitive information.
- Utilize a reputable VPN for added anonymity.
- Research onion links thoroughly before clicking.
- Remain vigilant about the latest dark web threats.
Onion Links: Accessing the Forbidden Knowledge
Delving into the shadowy realm of Onion Links is a perilous journey for any intrepid soul. These hidden gateways, veiled in layers of anonymity, offer bits of knowledge long forbidden. Brave users navigate through a labyrinthine network, searching for secrets that lie beneath the surface. However, beware, for the path can lead to dark destinations.
- Caution
- Truth will set you free
- The choice is yours
Dissecting an Onion Link
An onion link can be described as a approach used to obscure the ultimate destination of a web request. This layered structure involves multiple hops, each navigating to a subsequent endpoint. The onion link's primary function is to protect the privacy and anonymity of users by fragmenting the straight path between them and their goal.
- Typically, onion links are linked with networks like Tor, which prioritize user privacy.
- Each layer in an onion link encapsulates a individual address.{
- Ultimately, the final layer of the onion link reveals the actual destination, completing the journey.
Navigating the Deep Web: Cybersecurity in Onion Link Territory
Onion links, entrance points to the hidden corners of the internet, present a compelling paradox. On one hand, they offer obscurity, shielding users from monitoring and fostering open dialogue. However, this very cloak also attracts malicious actors who leverage onion links to engage in cybercrime. From hackers seeking to exploit vulnerabilities to con artists preying on unsuspecting users, the dark web, accessed via onion links, poses a significant threat to cybersecurity.
- Individuals must exercise extreme caution when encountering onion links, double-checking authenticity before diving in.
- Robust security protocols| are indispensable for mitigating the threats associated with onion link usage.
- Cybersecurity literacy among users is paramount in navigating the complex landscape of cybersecurity and onion links.
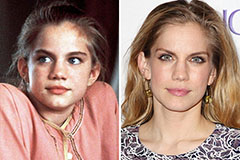 Anna Chlumsky Then & Now!
Anna Chlumsky Then & Now! Keshia Knight Pulliam Then & Now!
Keshia Knight Pulliam Then & Now! Michelle Trachtenberg Then & Now!
Michelle Trachtenberg Then & Now! Nancy McKeon Then & Now!
Nancy McKeon Then & Now! Samantha Fox Then & Now!
Samantha Fox Then & Now!